Okay, this is going to be my last post on hacking your Magicjack, as all my messing around is seriously pissing my wife and colleagues at work off. It takes a little finagling to get this working. If you have a heavy duty firewall like a Cisco ASA, then you will have to modify this setup a bit which I will cover later. The reason is that enterprise Firewalls may consider my setup as a possible LAND Attack and will drop packets. However, if you can afford a Cisco ASA, then you probably can afford a real telephone solution anyway. No, this post is more geared for the SOHO network using a simple Linksys or D-Link type router. This is more of an ideal solution, as that is how Magicjack is designed. I will still give you a tip on how to get it working behind a Cisco ASA ;-P
Once again, as previously stated, this violates Magicjack’s TOS. Perform this setup at your own risk. I accept no responsibility!
So here is what you will need for this project:
- Windows Server
- Magicjack Password/Proxy Info
- 3CX PBX
- MJMD5
- 3CX Softphone (Or any SIP phone that 3CX supports)
Now I will not get into the install portion of 3CX, as it is pretty easy, but if you must see how it is done, here is a clip from Hak5 Episode 503 where Matt Lestock shows us how to install 3CX and have it basically up in running in about 10 minutes.
After you have 3CX setup, we need to get our proxy going. In a SOHO environment, we can set it up on the same server as 3CX. To do that download MJMD5, and extract it to C:\MJMD5. Run it once to configure your settings and select the option to save the settings (See part one for more info). MJMD5 will save your settings in an INI file that it will now use as it’s defaults. Once you have that configure a scheduled task to run as SYSTEM to kick off MJMD5.exe at start up. You will now have MJMD5 basically running as a service!
Now that we have that running as a service, you will need to open the following ports on your firewall to point to your 3CX/MJMD5 Proxy server:
- 5060 UDP
- 5070 UDP
- 3478 UDP
- 9000-9003 UDP (Higher for more phone connections)
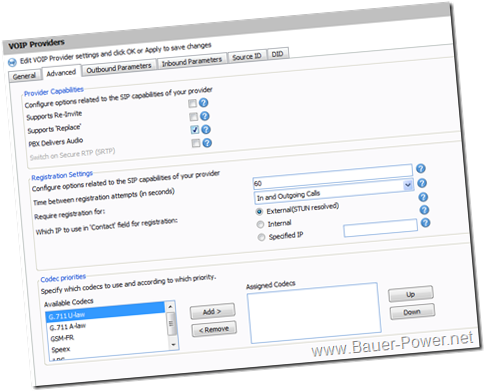
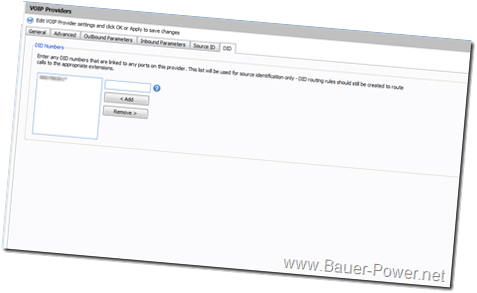
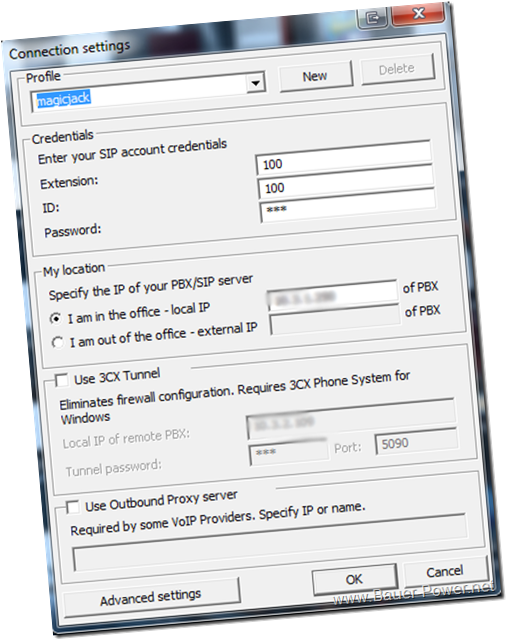
With those ports open we need to configure our SIP trunk to point back at our 3CX server using our Public IP address. You should have the following settings under VOIP Providers (Click for larger images):
Note that the IP address in the first picture needs to be your public IP address. Your Authentication ID and Password will be your Magicjack username and password.
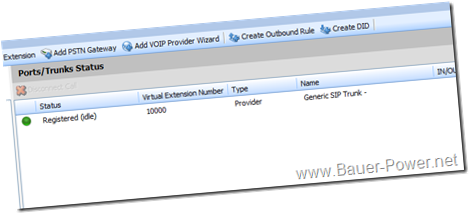
Once that is working correctly, you should see that your SIP trunk is now active:
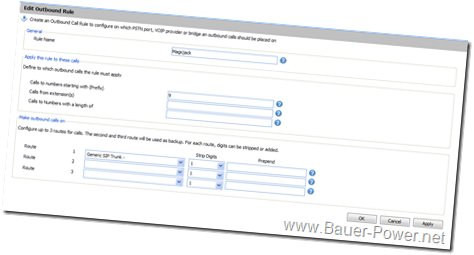
before you can make outbound calls, you will need to create an Outbound dialing rule. The simplest method is shown below which makes it so people need to dial a 9 before dialing an outside line.
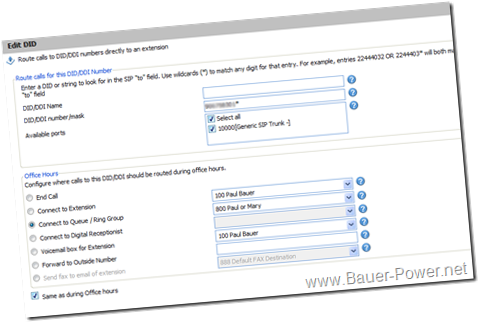
 You probably want people to call you too right? For that we need an inbound rule. For that, all you need is to set it up similar to mine with your Magicjack number minus area code and an asterisk next to it. For example 1234567*. After that you have to specify a destination extension. I created a ring group so both my wife’s phone and my phone ring at the same time. You can set yours up however you want.
You probably want people to call you too right? For that we need an inbound rule. For that, all you need is to set it up similar to mine with your Magicjack number minus area code and an asterisk next to it. For example 1234567*. After that you have to specify a destination extension. I created a ring group so both my wife’s phone and my phone ring at the same time. You can set yours up however you want.
That is about it. Now you have a working PBX at your home office or small office using a $20 per year SIP trunk as the connection!
I mentioned setting this up using a higher grade Firewall like a Cisco ASA. For that to work you will have to have a second server on the same subnet to act as the proxy server. The reason being is that really good firewalls will drop packets if the source packet comes from an IP address on the internal network. They think it is what is known as a LAND attack.
When I did my testing I first used my D-Link wireless N router at home, so the SOHO scenerio worked fine. For my lab at work I setup mjproxy on a Linux server. I mentioned how to do that in Part 3. The only difference was I created a shell script and added it to rc.d to run as a daemon at startup. If you aren’t Linux savvy, you can do the Scheduled task trick on another Windows server on the same subnet. Either way, 3CX needs to point to the proxy server’s internal IP address for SIP authentication. In both cases, ports 5070 need to point to the proxy server no matter if it is hosted on the same server as in the SOHO example, or on a different server in the Cisco ASA example.
Now that our server is setup, we are ready to attach a phone. I used the 3CX softphone for my testing. I like how it looks like an iPhone! Also, it is designed to work natively with 3CX. Here is a screen shot of my config Make sure you point your phone to your 3CX server, not Magicjack!:
Here is a look at the softphone itself:
I am still playing with my setup at home. If you try this out, and something isn’t working, hit me up in the comments!


 1:00 AM
1:00 AM
 El DiPablo
El DiPablo